Latest threats like the already known WannCry ransomware show today, like never before, that organizations must concentrate more intensively on complementary approach to IT Security and that having obsolete solutions that were good a decade ago can bring tragic effects on brand image or even cause the bankruptcy of the biggest enterprises.
Standard, legacy approach
The legacy security approach, which is still common in many organizations, concentrates mainly on securing Internet Edge network segment with stateful firewalls. This would often help to prevent traffic initiated from “Internet” from getting to the trusted / private side of the firewall. This was effective earlier but is not good enough today. Another solution – very often the “Mount Everest” for companies – is usage of 802.1x protocols in network access layer securing against unauthorized user access, but nothing more.
The big shift from commerce to e-commerce and the digitalization process of people’s lives has made the security business more sophisticated and remarkable. Worldwide cybersecurity market grew from $3.5 billion in 2004 to $75 billion in 2015, forecasted to reach $170 billion by 2020 (source: http://cybersecurityventures.com/cybersecurity-market-report/) so the more sophisticated attacks arise, the more sophisticated security response should be.
Threats evolve
There are many flavors of threats which include different attack types. Attacks on a high level can be differentiated on methodology and motives. In the late 80s, the first serious attempts to attack/infect individual PCs were seen like the Robert Tappan Morris worm which infected about 6k computers within hours in 1988. During this period the tendency was to write viruses and trojans to disrupt computer operations and attempts were made to spread randomly the first viruses without a specific aim. Then in the mid-90s hackers started to write codes to analyze user’s activity (called spyware). In 2000, the year of e-commerce expansion, e-commerce giants like Amazon, eBay and Yahoo were highly affected by Distributed Denial of Service (DDoS) attacks – which caused the outage of those company’s Internet Services. With the growing popularity of social networks, the attack techniques have started to become more focused on stealing user data, conversations, financial details with the help of social engineering approach to gain control over the user device. All the known attack methods are as good as long as they are successful, but this leads to a serious potential risk that a well-prepared attack can affect, for example, nuclear reactors or national security or health systems or even worldwide flight schedule.
Today’s attacks are performed using frameworks and attack cycles, like APT (advanced persistent threats), which can be motivated by business, political or cultural reasons. An APT has the following phases:
- initial compromise
- foothold establishment
- privilege escalations
- reconnaissance
- move
- maintain
- complete
A well-prepared attack can be very disruptive, where there might be a high possibility of loss of corporate or public image, losing sensitive data like a list of partners and customers or credit card numbers. That is why security approach and solutions need to take into account all above aspects to be effective.
Anatomy of today’s most dangerous threats
The latest example from our ground is the WannaCry ransomware which on May 2017 infected many Windows operating systems by spreading across the network, exploiting end user machines one by one and encrypting files wanting the ransom for data decryption possibility. What is so interesting in this kind of malware? Because malware’s nature is the ability to move and infect other computers within the same subnet it can be very serious destroyer that can spread without any human intervention. #WannaCry scans the subnet looking for #445 TCP port which is default port for SMB services, and if 445 is found open then #EternalBlue exploit infects the machine and installs the #DoublePulsar to take the control over machine. In parallel there could be observed C2 callbacks (C&C connections) to the Internet based hosts.
In some situations so called Point-In-Time detection solutions like Internet Edge IPS or Firewall with IPS services can protect against threat especially where signature is documented, behavior is known or payload structure is obvious. But malware could be more sophisticated. By using sleep techniques, encryption or polymorphism, Point-In-Time solutions might not be able to detect such threats.
Sometimes legacy systems are not able to react or even alert security team for weeks and hackers have time to start the privilege escalation and reconnaissance process. In such situations, the anonymous activity is invisible to corporate systems or IT team for many days. It means there might be intruders documenting and penetrating your infrastructure for long duration and no one knows about it.
The market response
Because legacy firewalls, IPS, VLAN segmentation of the network or anti-virus definitions might be not sufficient today, it is really challenging to choose the right solution.
There has been a “battle” since the first threats arose where we have one side which writes the threats and the other side which writes the antidote like antiviruses, antimalware, intrusion prevention systems signatures and so on. The most challenging aspects of today for IT teams and security solutions is the fact that first: there is a rising volume of data that is traversing the network encrypted using SSL and IPSec thus making harder to inspect in terms of malicious code recognition and second: that malware itself is more intelligent and know how to cheat the IPS/Firewall.
Because of above, besides the security appliances or prevention techniques up to date signature subscriptions there is a need for complex solution that can analyse the traffic and user behavior, correlates the facts and react just in time.
Complex Security Solution example against modern threats
Complementary solutions
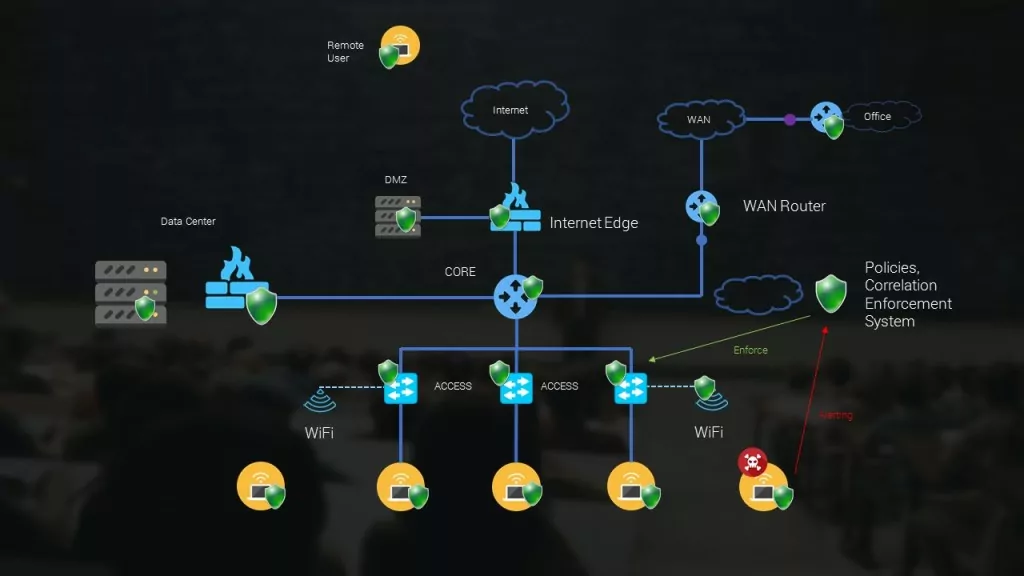
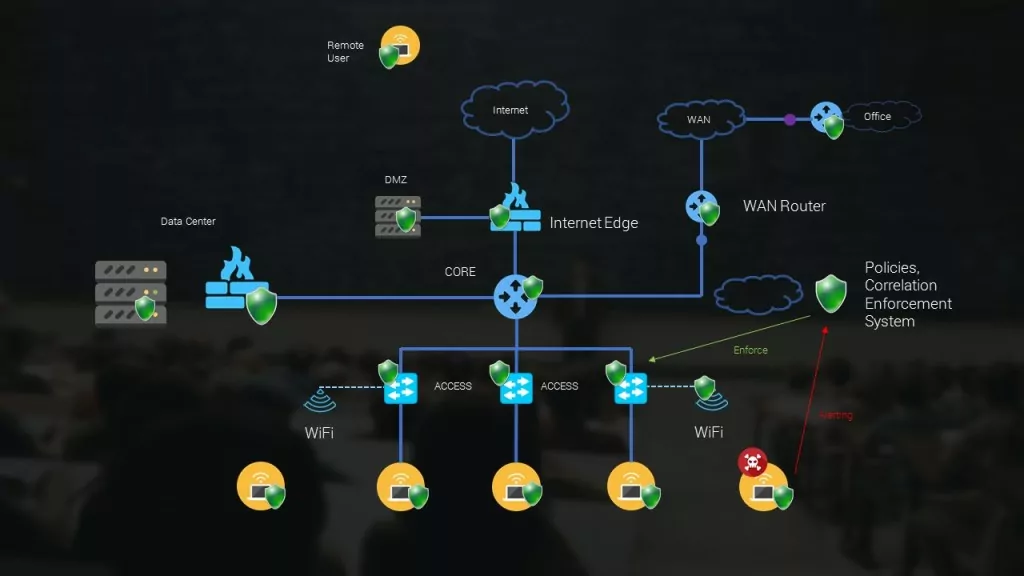
Security solution needs to cover and monitor all areas of network, detect the threat even sophisticated and quarantine machine or system if already infected to prevent spread. In short it needs to cover all aspects of threat life cycle. That is why security solution components must cooperate.
To verify if your solution is prepared try to answer the following questions:
- How are the end point machines protected?
- If the network is ready to monitor the suspicious non-standard behavior?
- Or it is only signature-based for Point-In-Time reactions?
- If there is NGFW on the path with Antimalware functions?
- How quickly the system can respond to Zero Days?
- How system reacts to exposed threats?
- How efficient is the quarantine or isolation of infected components?
- If the above is automated?
If we want to secure corporate services from being compromised we need to think globally and sometimes think like an intruder. We need to secure the whole path from the Internet to the User device OS and whole infrastructure segments. The best option is that whole network and system components behave like one organism thus preventing or reacting will be effective. In the following posts, we will review market solutions that are complementary and satisfy the above requirements. Stay connected!






Leave a Reply