After we prove that CPU utilization can be easily increased by anyone a time (as shown in the previous blog post, “Protect the Control Plane – part 1, trivial attack.”), I feel obliged to show how to quickly prevent the cause of potential network and service damage. I will use the Cisco Cat6500 example, but of course, the technique and idea apply to other vendors (if the vendor supports it).
Cisco in IOS/XE/XR operating systems gives the Control Plane Policing (CoPP) and Control Plane Protection (CPPr) mechanisms. Not going into detail at the moment those two techniques rely on policing unwanted traffic, but both techniques differ. The approach in CoPP puts the policing on aggregate traffic going into the CPU, the CPPr makes the policing more granular and divides the traffic into three types (host, CEF-exception, and transit). I will explain those approaches in detail later on. Implementing CoPP/CPPr is like building QoS with MQC (Modular QoS CLI).
To limit ICMP spikes,
1. Define the icmp traffic types with acl and class maps:
ip access-list extended icmp
ip icmp any any
class-map match-all CoPP_ICMP
match access-group name CoPP_ICMP
2. Define a policy map
policy-map CoPP
class CoPP_ICMP
police cir 32000 bc 1500 be 1500 conform-action transmit exceed-action drop violate-action drop
class class-default
police cir 10000000 bc 312500 be 312500 conform-action transmit exceed-action transmit violate-action transmit
3. Apply
control-plane
service-policy input CoPP
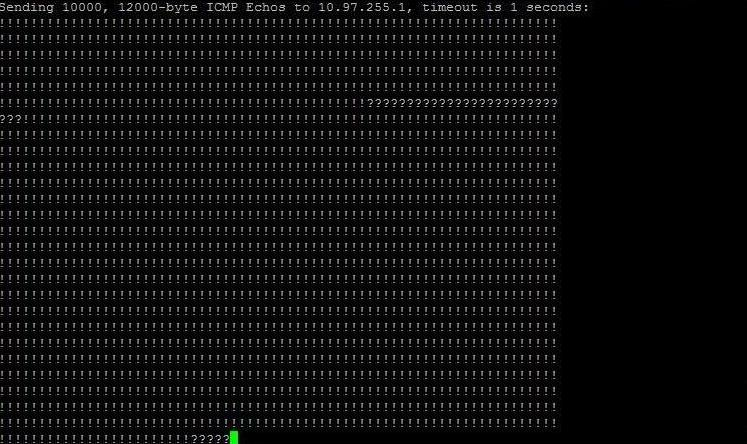
Testing this we used simultaneous Windows7 based ICMP (regular ping) and ASA sourced large size ping packets. Screen from ASA output during CoPP applying process shows clearly the moment:
See that Windows ICMP is not changed because of policing (limit the receiving packet rate), not dropping the input traffic.
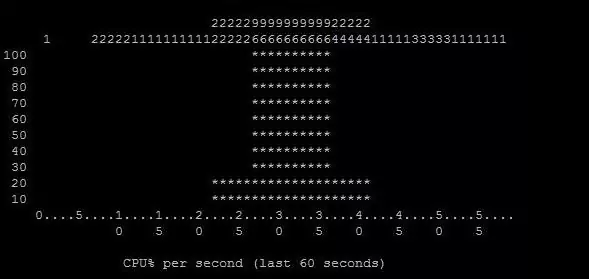
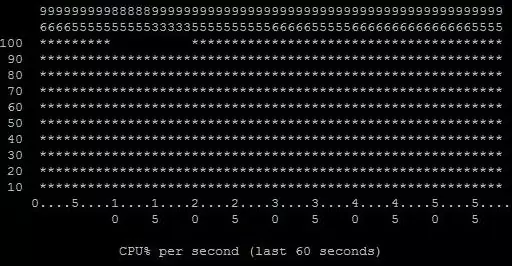
Now from the network Core point of view, it is clearly seen the CPU spike (moment of DoS) and normalization (moment of CoPP application):
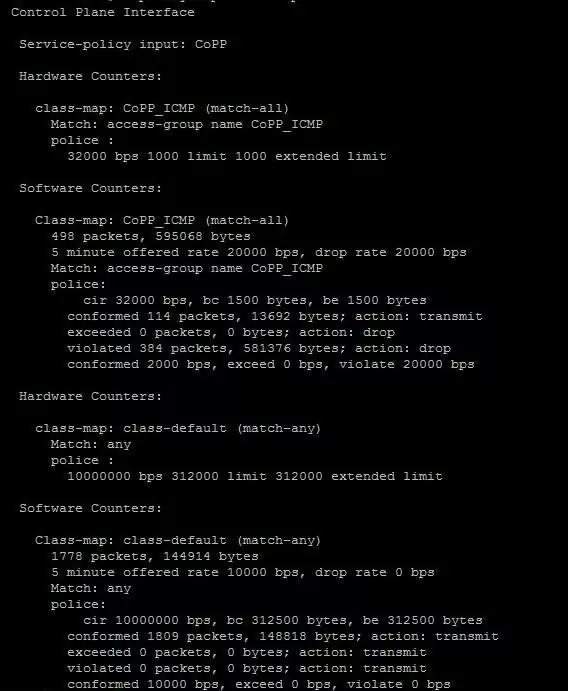
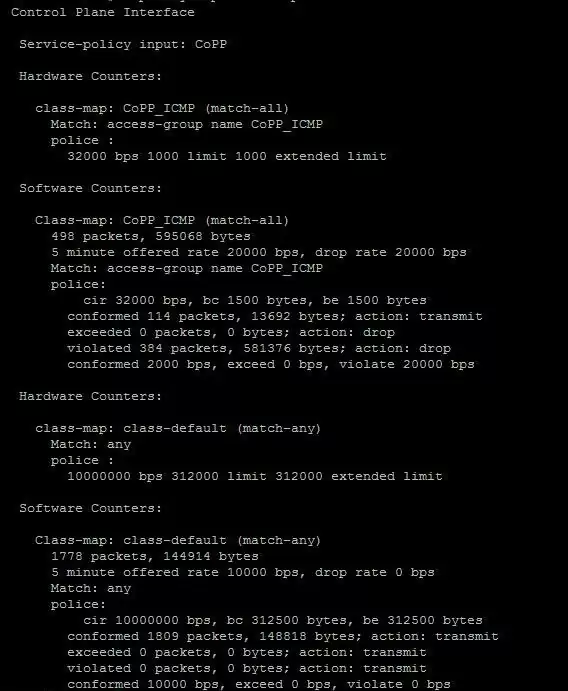
And policy map counters show all violating packets and confirm packets.
So far so good. Later, I will concentrate on building a “best practice” full control plane security policy. But is worth underlining that the above policy doesn’t care about the remaining control plane traffic (class-default hs transmit actions even for violating traffic).
Notice: Use CoPP and CPPr carefully. Using those techniques without a theory background can cause outages of network services including management communication with devices.